Monitoring RDP access is the key to securing your IT infrastructure and reducing risks associated with remote access. This article provides a brief overview of the benefits and best practices of RDP session monitoring and shows how to monitor RDP connections on servers, jump hosts, and any other endpoint protected by Syteca. It’s equally useful for those already using Syteca and anyone who wants to familiarize themselves with the platform’s capabilities.
Key takeaways:
- RDP session monitoring provides you with visibility into remote access, therefore minimizing security risks, simplifying compliance, and accelerating incident response.
- Secure, compliant RDP oversight should include alerts for high-risk events, automated responses to potential compromise, and regular audits.
- Syteca enables you to secure RDP connections to your IT infrastructure by allowing you to:
- Configure alerts on RDP connections
- Record remote desktop sessions
- View and block sessions in real time
- Audit recorded sessions
- Export sessions for forensic analysis
- Generate reports on RDP session activity
Why monitor RDP sessions?
With strict data protection regulations and increasing audit demands, monitoring RDP sessions is vital to maintaining transparency, accountability, and compliance across your remote access environment. Continuous visibility into remote access also helps organizations track user behavior and significantly reduce the risk of security breaches.
Benefits of monitoring and recording RDP Sessions
These are the key benefits you get from monitoring remote user sessions and connections to your critical endpoints:
Benefits of monitoring and recording RDP sessions
Mitigate cybersecurity risks
Maintain cybersecurity compliance
Increase visibility. RDP session recording and monitoring provide visibility into remote user behavior on critical endpoints. It helps identify who is accessing the system and when, as well as what actions they are performing. RDP recording can also help you collect evidence for investigating security incidents.
Mitigate cybersecurity risks. Increased visibility can help you detect any suspicious or unauthorized remote user activities that may pose a security risk. You will also be able to proactively identify potential cybersecurity risks, such as insider threats, and take appropriate measures to mitigate them.
Maintain cybersecurity compliance. Monitoring user activity is often a requirement of cybersecurity standards, laws, and regulations such as HIPAA, ISO 27001, SOX, and PCI DSS. Remote desktop monitoring enables your organization to meet these requirements, secure sensitive data, and avoid potential penalties or legal consequences.
Respond to incidents. Monitoring remote user activity enables you to promptly detect and respond to cyber threats. With real-time RDP session monitoring, you can immediately act to mitigate the impact of security incidents, investigate their root cause, and prevent further damage or data breaches.
Get a Syteca online demo!
See how Syteca helps you manage remote access security risks.
Best practices for secure and compliant RDP monitoring
RDP monitoring should focus on timely threat detection, incident containment, controlled evidence handling, and consistent reporting to ensure remote access is both manageable and auditable. Below are the best practices to follow when monitoring RDP sessions:
- Use event-based alerting. Set alerts on suspicious activity, such as uploading files to cloud storage services, entering specific keywords, or installing unauthorized applications.
- Record based on risk and context. Prioritize the monitoring of privileged users, third-party access, and activity on critical endpoints.
- Protect sensitive data. Pseudonymize or mask sensitive information in session metadata and reports to reduce privacy risks.
- Enable live session oversight. When an event triggers a security alert during an active session, review it in real time to establish intent and contain issues quickly.
- Automate containment of high-risk events. Apply automated response actions, such as user blocking, when clear signs of compromise are detected and prevent escalation without prolonged manual intervention.
- Regularly review session activity. Ongoing analysis of sessions, alerts, and suspicious actions helps you separate legitimate activity from remote access misuse.
Next, let’s look at how Syteca helps you implement these best practices.
Using Syteca to monitor RDP sessions
Syteca is a privileged access management (PAM) platform with built-in identity threat detection and response (ITDR) designed to protect your organization against access-driven threats.

Syteca is a flexible solution with a range of deployment options. The platform lets you track and record user sessions across all endpoints, supporting remote desktop user activity monitoring organization-wide.
Without further ado, let’s see how you can monitor remote desktop sessions and record RDP sessions in your IT infrastructure with Syteca.
User Activity Monitoring (UAM) with Syteca
Monitor and record RDP sessions
By default, monitoring sessions are enabled for local and remote users on endpoints with the Syteca software agent installed.
If you only need to monitor remote employees, third-party vendors, and other external users, you may prefer to record only the corresponding sessions. In this case, you must set up the IP filtering feature on the target endpoint.
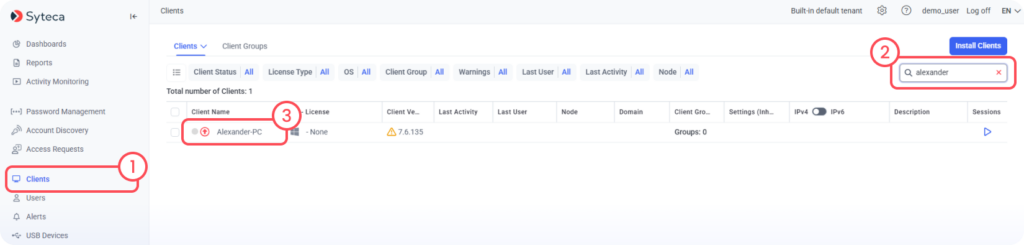
To exclude recording of internal user sessions on the selected endpoint, open the Clients page.
Easily search for the required endpoint by keyword. Then, click on the endpoint’s name in the Client Name column.
Open the Remote Host IP Filtering tab.
In the Filter State drop-down menu, select: Monitor activity from all remote public IP addresses except
In the field below that, enter the IP addresses of internal users’ computers that don’t require monitoring.
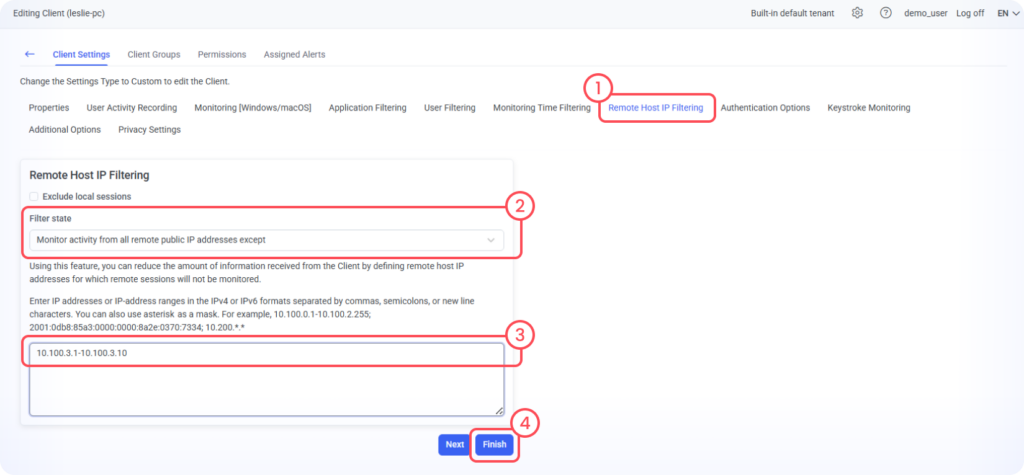
Click Finish to save settings. Syteca will now monitor only remote user connections to your endpoints.
Third-Party Vendor Security Monitoring with Syteca
Mask sensitive data in user sessions
When monitoring remote users, it’s essential to ensure the proper protection of sensitive data like passwords, credit card numbers, and Social Security numbers. Syteca automatically masks sensitive data in real time.
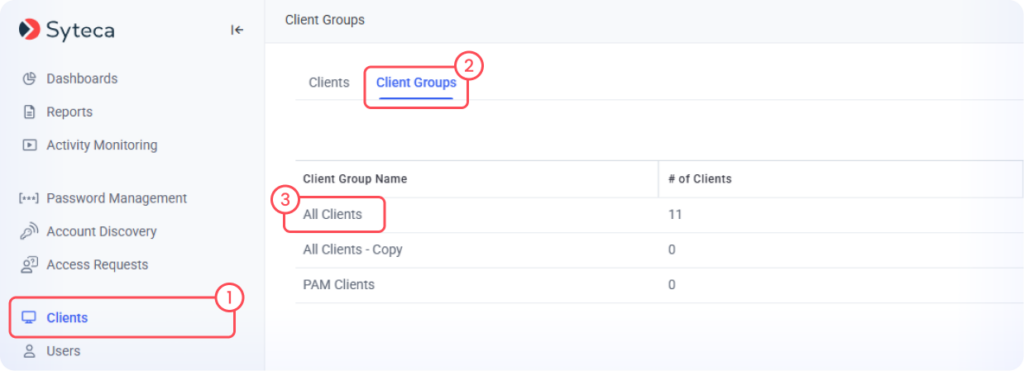
Suppose, for example, you need to enable sensitive data masking on all computers. To do this to the Clients page, click on Client Groups, and select All Clients.
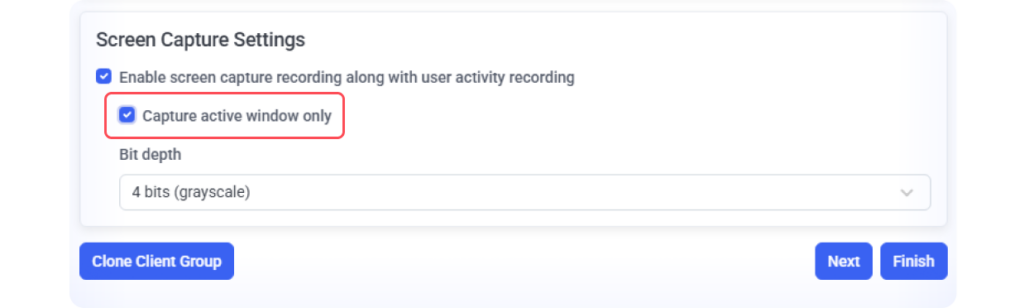
This will bring up the Group Settings editing window. Click the User Activity Recording tab and scroll down to Screen Capture Settings, and click the box next to Capture active window only.
Then switch to the Privacy Settings tab and toggle Enable Sensitive Data Masking.
Click Add to define regex rules for the sensitive data you want to mask. For example, you can mask Visa & Mastercard card numbers. Each rule must have a name and a valid regex pattern.
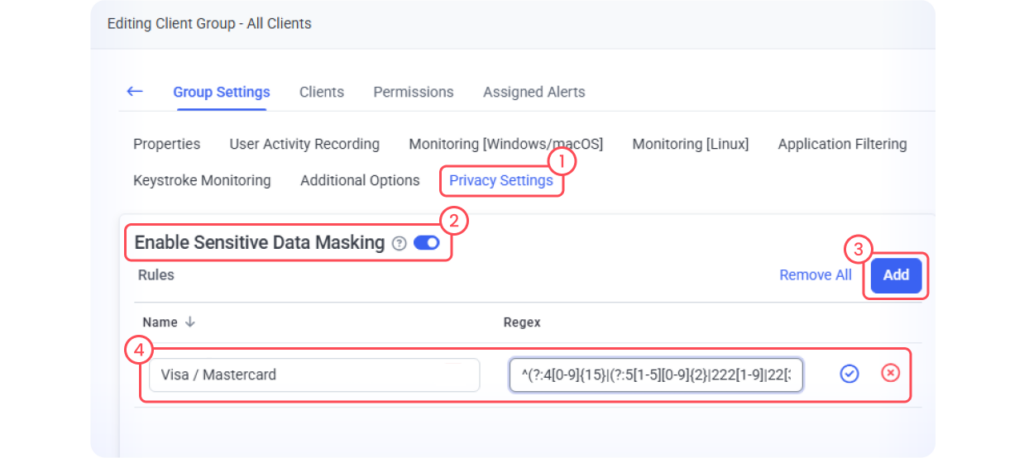
Once saved, Syteca will begin scanning screen captures, clipboard activity, and keystrokes in real time. When a match is detected, the data is masked automatically in both the Session Player and metadata.
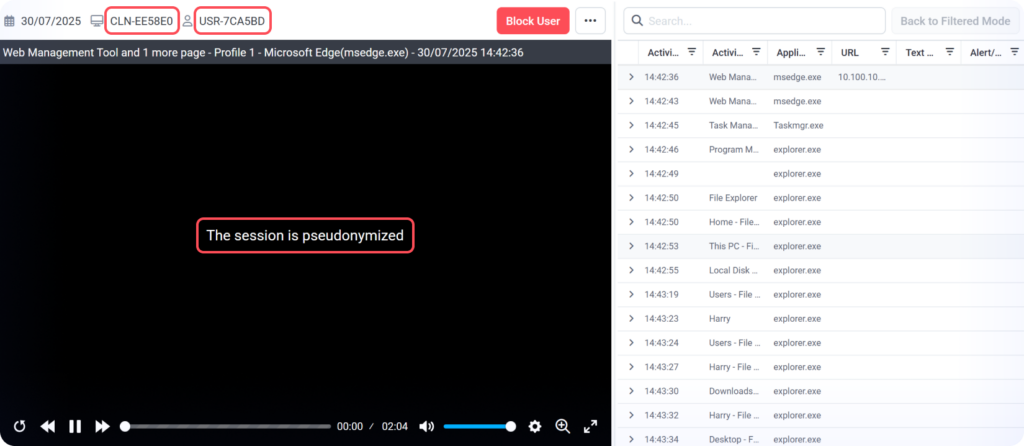
To further enhance privacy protection, Syteca provides a Pseudonymizer feature that hides users’ personally identifiable information recorded during RDP session monitoring.
In Pseudonymized mode, personal data is concealed from administrators, unless it’s needed for investigations and access to it has been explicitly approved by a Supervisor. This functionality can be activated upon request via your Syteca vendor or Support Team.
Here’s what a recorded session looks like when the Pseudonymizer is activated:
Receive notifications on RDP connections
When dealing with a highly critical endpoint, you may want to not only record user sessions but also receive real-time notifications whenever an RDP connection is established.
To do so, open the Alerts page.
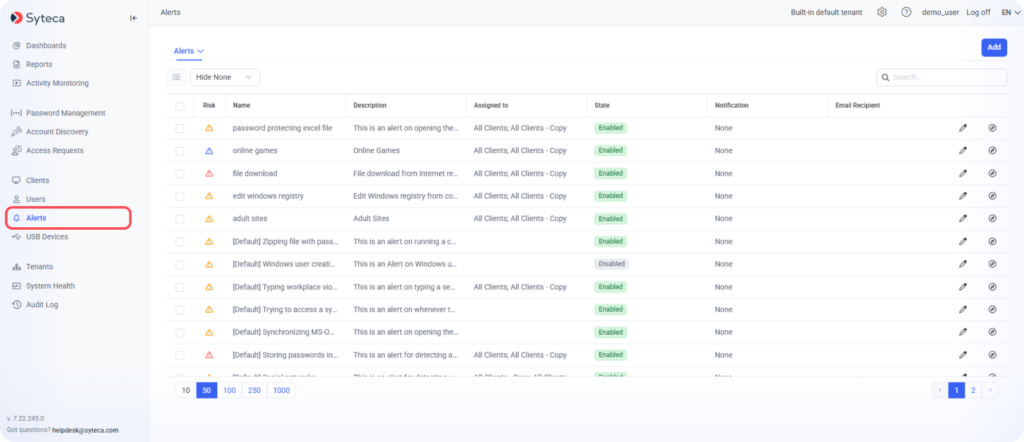
Syteca has a comprehensive incident alert system with a list of default alerts that cover some of the most common use cases and cybersecurity threats.
The alert needed is the Session start alert. To quickly find it, type in the alert’s name in the search box.
Click the Edit Alert icon to configure this alert.
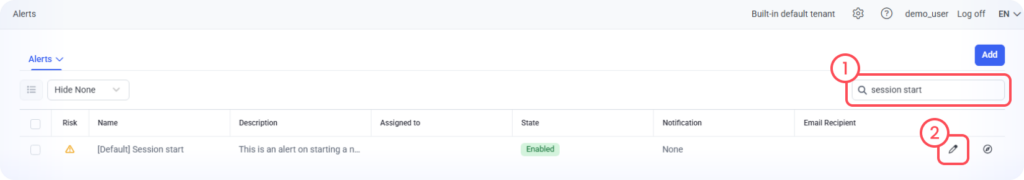
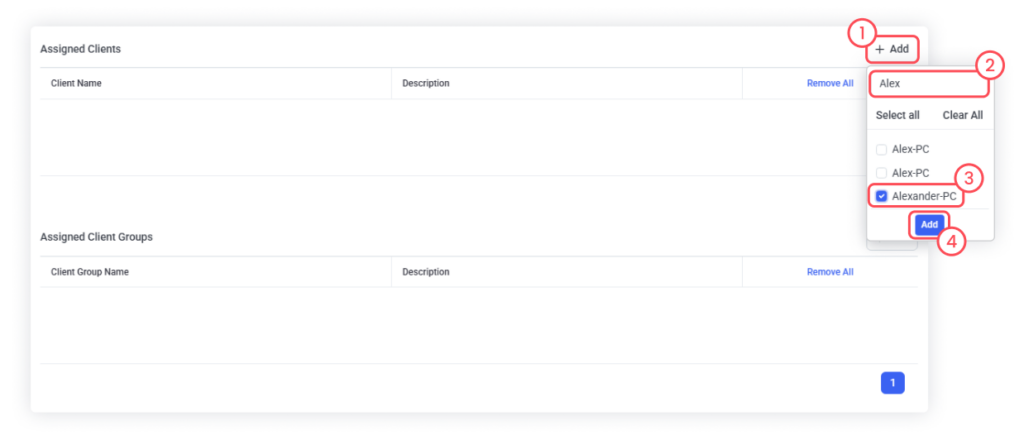
In the Assigned Clients section, click Add to add the server or other computers on which incoming remote connections must be detected.
In the Actions section found below, you can configure the alert notifications and additional actions to be performed when an alert is triggered.
Select the Send emails to option and enter the email address notifications will be sent to.
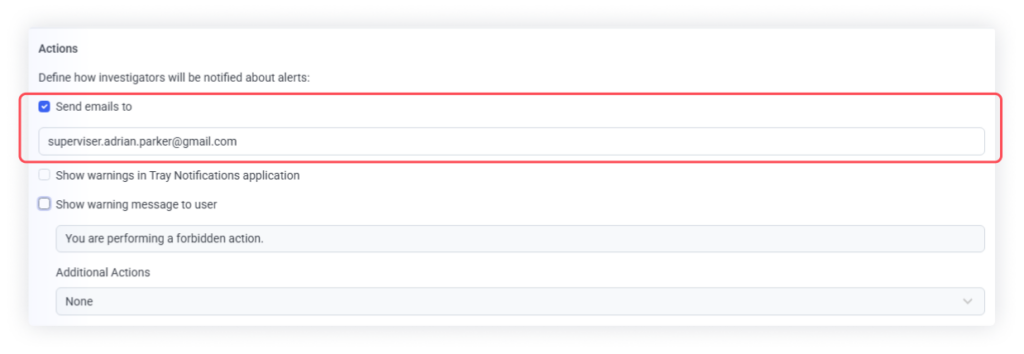
Then click Finish. You will now receive an email each time a remote connection to the selected server is established.
You can set up additional alerts to receive notifications on suspicious behavior by your local and remote users. For example, you may choose to receive notifications when a remote user tries to upload a file to the cloud, enters a specific keyword, or installs an application.
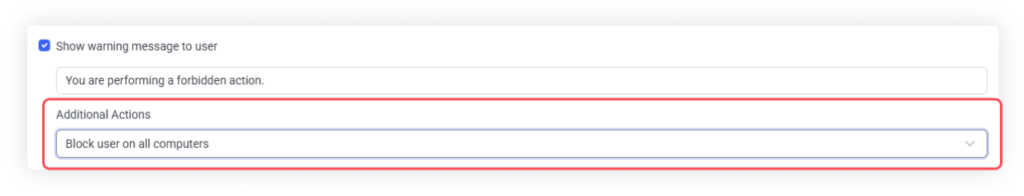
In addition to notifications, you can configure the system to respond automatically to certain actions by blocking a user, displaying a warning message, or killing the process.
View and block remote desktop sessions in real time
Let’s suppose that you get an email notification about a remote third-party user connection to your server. You can open the session via the direct link provided in the email.
Session Player allows for viewing remote desktop sessions by letting you review the screen recording alongside metadata.
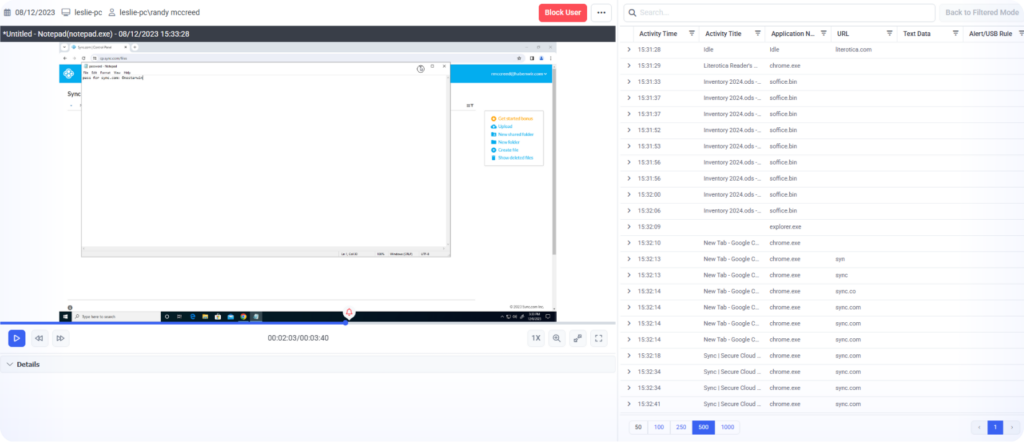
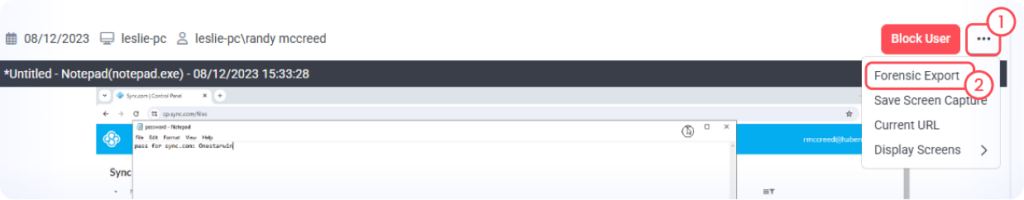
If a remote user is still connected to your server via an RDP session, you can view what the user is doing in real time by clicking the Live button. This can help you implement the four-eyes principle, which states that any external user activity that introduces potential risks must be reviewed by a second person.
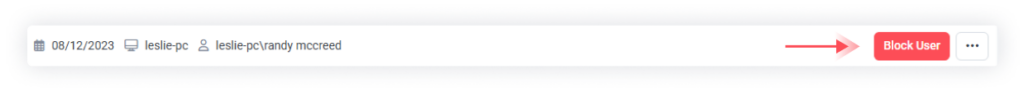
If a user is performing potentially harmful or prohibited actions, you can block them by clicking the Block User button.
Click the Live button again to stop playing the Live session.
View and audit recorded RDP sessions
Now, let’s see how to view remote desktop sessions that have been previously recorded on the monitored server.
On the Activity Monitoring page, you can filter sessions by server name.
In the session grid, you can view information about remote connections, such as the names and IP addresses of remote computers connected to the server.
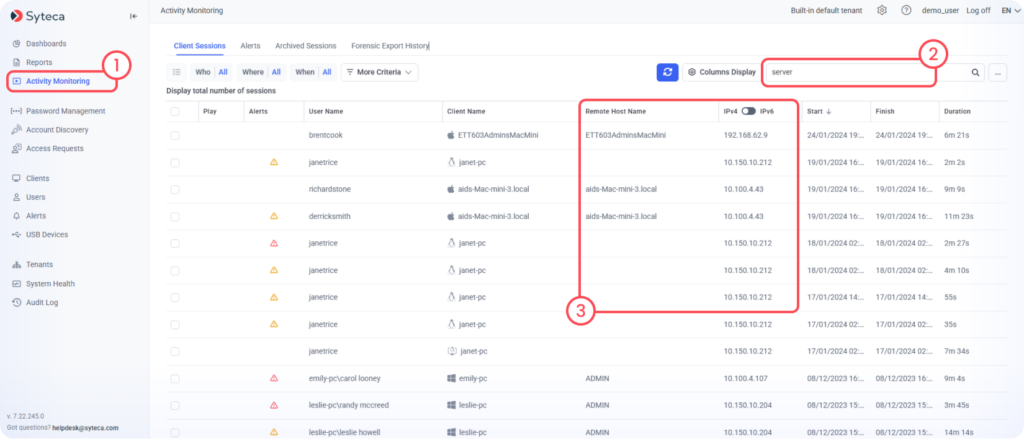
Double-click the session to view screen recordings and more details in the Session Player.
Export user sessions for investigation purposes
You can export sessions in an encrypted format to view session data on any computer, even without access to the management tool.
Open the session you want to export. In the Session Player, click the ellipsis menu and select Forensic Export in the drop-down list.
In the pop-up window, define the necessary settings and click Forensic Export. You can protect the exported session with a password.
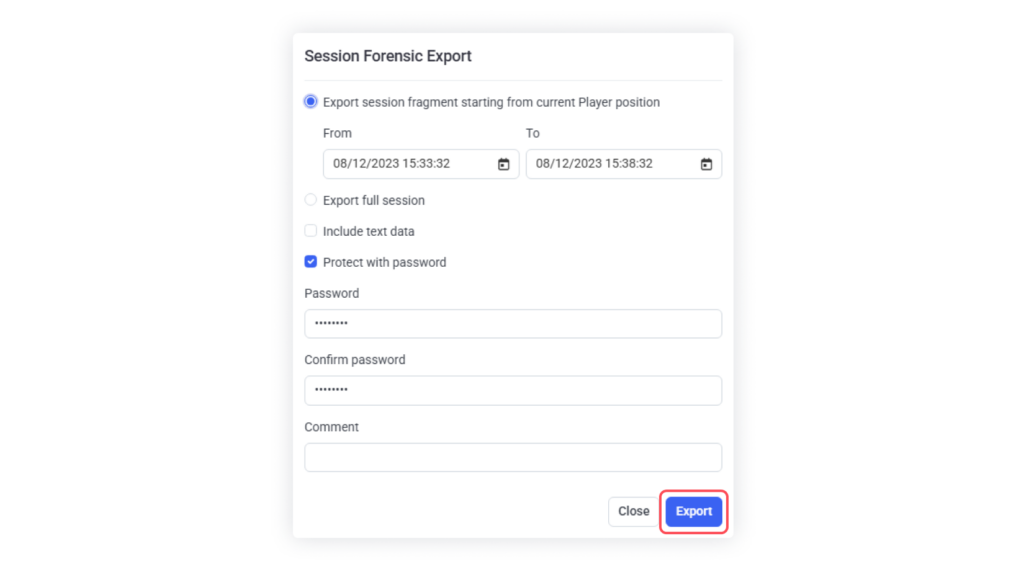
As soon as the export finishes, you can download the resulting file in the Forensic Export History tab.
Note: You will need to download the Syteca Forensic Player to view the exported session.
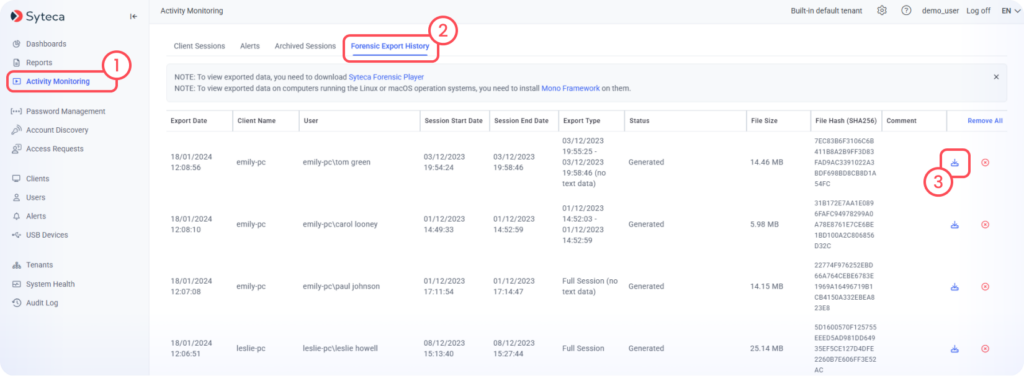
You can verify the integrity of an exported session using the SHA-256 file hash displayed on the same tab.
Generate reports on RDP connections to your endpoints
Syteca enables you to regularly receive all necessary information about remote connections to the server in a summary report. You can generate reports ad hoc or have them sent to your email according to a schedule you define.
To do this, open the Reports page and select Session Grid Report in the Report Type drop-down menu.
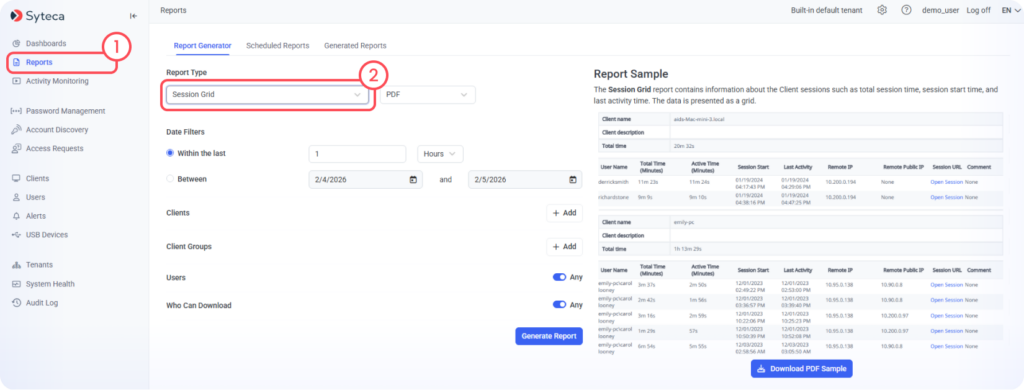
You will see a sample and description of the selected report on the right.
Click Add in the Clients section and select the endpoints for which the report will be generated. You can search for endpoints in the search box.

Define other options and click the Generate Report button to get the report.
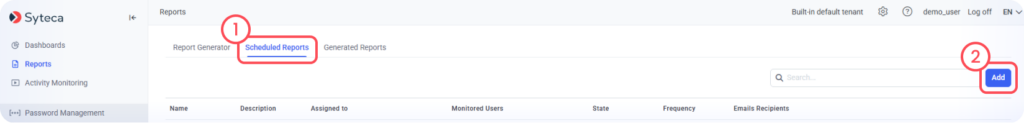
To schedule the report, open the Scheduled Report tab and click Add.
On the opened Add Rule page, select the Enable scheduled report generation option, enter a name for the rule, and click Next.
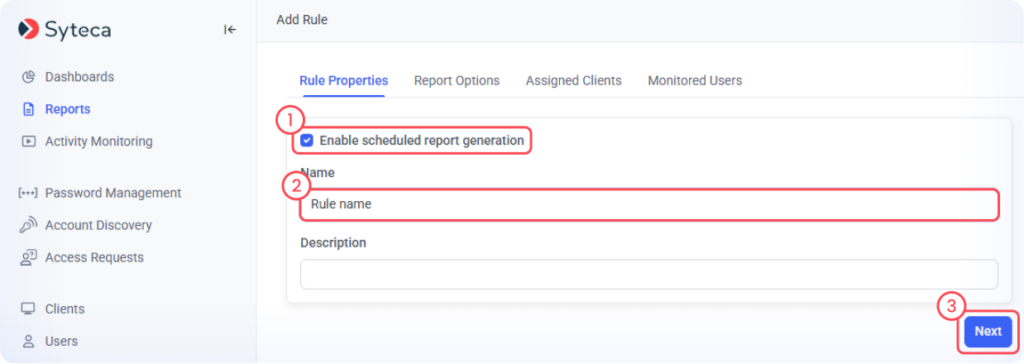
Set the report parameters, enter the email address to which the report should be sent, specify clients and users to include in the report, and click Finish.
The report will be automatically generated and sent to your email address according to the defined frequency.
Case study
An HVAC Service Provider Secures Data and Maintains Employee Productivity after Switching to Remote Work

Boost the security of RDP connections to your infrastructure
Well-established remote desktop session recording and monitoring increases visibility into user activities, helps mitigate cybersecurity risks, ensures your organization’s compliance with cybersecurity requirements, and enables you to respond effectively to security incidents. Syteca provides controlled remote access and full visibility into RDP activity, allowing you to detect suspicious behavior as it occurs and respond immediately.
Privileged access management (PAM) helps you granularly control users’ access permissions, while native identity threat detection and response (ITDR) enables you to see what happens after access is granted so you can promptly detect and respond to security threats.

With Syteca, you can start managing identity-driven security risks and enhancing your organization’s overall cybersecurity today.
Want to try Syteca?
Request access to the online demo!
See why clients from 70+ countries already use Syteca.